Large Data Analysis & Innovative Data Scientific Research Huge Information Researcher Full Arcitura Online Shop There can be no Internet Protocol (IP) or necessary gain access to control (MAC) address in a simultaneous source group. A general-purpose, top-level shows language developed for developing computer system operating system software program. It makes every effort to integrate the power of assembly language with the convenience of a top-level language. Offering procedures in which the included parties are a venture, which supplies products or services, and a consumer.
Spotlight: Data Quality-- Dimension 3, Precision
Initially created for IBM mainframes, many implementations have actually been developed for mini- and microcomputer database applications. SQL commands can be made use of to interactively collaborate with a data source or installed with a shows language to user interface with a database. Mathematical methods used with the collection, evaluation, interpretation and presentation of masses of mathematical information to recognize process variation and anticipate procedure efficiency. Examples consist of tasting techniques, analysis of difference, chi-squared examinations, regression analysis and process control graphes. The hardware, software and firmware utilized to carry out a software application engineering initiative. Typical components consist of computer system equipment, compilers, assemblers, operating systems, debuggers, simulators, emulators, examination devices, documentation tools and database administration systems.B 4 Control Commands
In bigger web applications, inputs can circulate from a frontend to an internal backend that supplies no feedback to the exterior. None of the previous approaches are applicable in this circumstance, known as blind XSS (BXSS). In this paper, we resolve this issue and provide the initially comprehensive study on BXSS. As no comments network exists, we verify the visibility of susceptabilities with blind code execution.Voice App Designer Experiences With Alexa And Google Assistant: Managing Threats, Obligation, And Safety
It additionally shares helpful coping devices, and aids the reader review their distinct connection with grief and loss. As you embark on this journey, bear in mind to remain interested and keep exploring new opportunities. The field of AI is ever-evolving, and there are constantly brand-new difficulties and chances to discover. We located that the alter towards strange nations in UPS is greater than that in HCI. Geographic and linguistic obstacles in the research approaches and employment approaches might create scientists to perform customer researches in your area. On top of that, lots of documents did not report participant demographics, which might impede the replication of the reported studies, causing low reproducibility. The Worldwide Impact Financial Investment Network (GIIN) defines influence financial investments as "inv ... Research reveals that SFDR PAIs protection spaces are a main challenge of SFDR conformity The European Union's Lasting Finance Disclosure Law (SFDR) could reinvent sustainability coverage-- and, in turn, rescope the information that business t. Little and mid cap firms have a fundamental part to play in conference EU Taxonomy purposes The Globe Health Company (THAT) is making use of World Wellness Day to put a focus on clean air. Clearness AI's ESG Impact Score measures how a company's procedures influence our setting and culture.- There's a strong demand for better supplier openness and even more education and learning for customers to make best use of the innovation's value.Control weaknesses can lead to threat not being decreased to an appropriate level in the appropriate task area (pertinent threat endangers accomplishment of the goals that are relevant to the activity location being checked out).Carries much less threat, such as high blood pressure cuffs and syringes, while Course II.b.Applying our pipe to 8,000 Android apps, we determined 17 third-party tracking SDKs that keep identifiers on outside storage.With the expansion of safety-critical real-time systems in our every day life, it is critical that their security is protected to assure their capabilities.
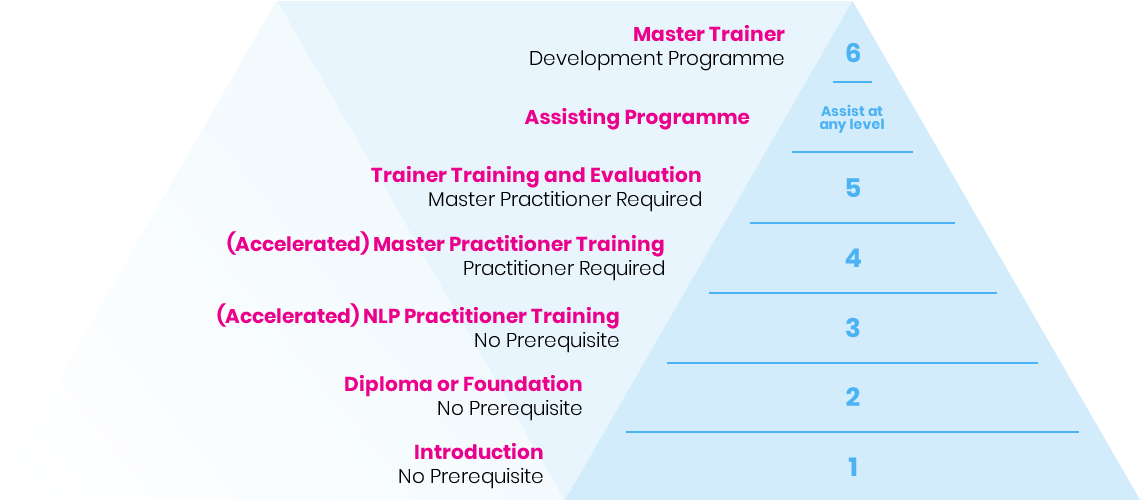
What are the 3 legs of NLP?